MFT Gateway is a hosted Software as a Service (SaaS) solution that enables file exchange over the AS2 or SFTP protocol, without the need to install or maintain.
- Blog
- AS4 Protocol in Healthcare 2026: Secure and Reliable Data
AS4
AS4 Protocol in Healthcare 2026: Secure and Reliable Data
Learn how AS4 ensures secure, reliable, and interoperable healthcare data exchange in 2026 with modern security and conformance standards.

Adeesha Jayasinghe
Published: 12 Mar 2026

Table of Contents
- AS4 Protocol in Healthcare 2026: Secure and Reliable Data
- The Technical Genesis and Standardization of the AS4 Protocol
- Core Security Requirements and Cryptographic Foundations
- Operational Reliability and Interaction Patterns
- The Role of AS4 in Regional Healthcare Ecosystems
- Implementation Challenges and Strategic Considerations
- Synthesis and Strategic Recommendations
AS4 Protocol in Healthcare 2026: Secure and Reliable Data
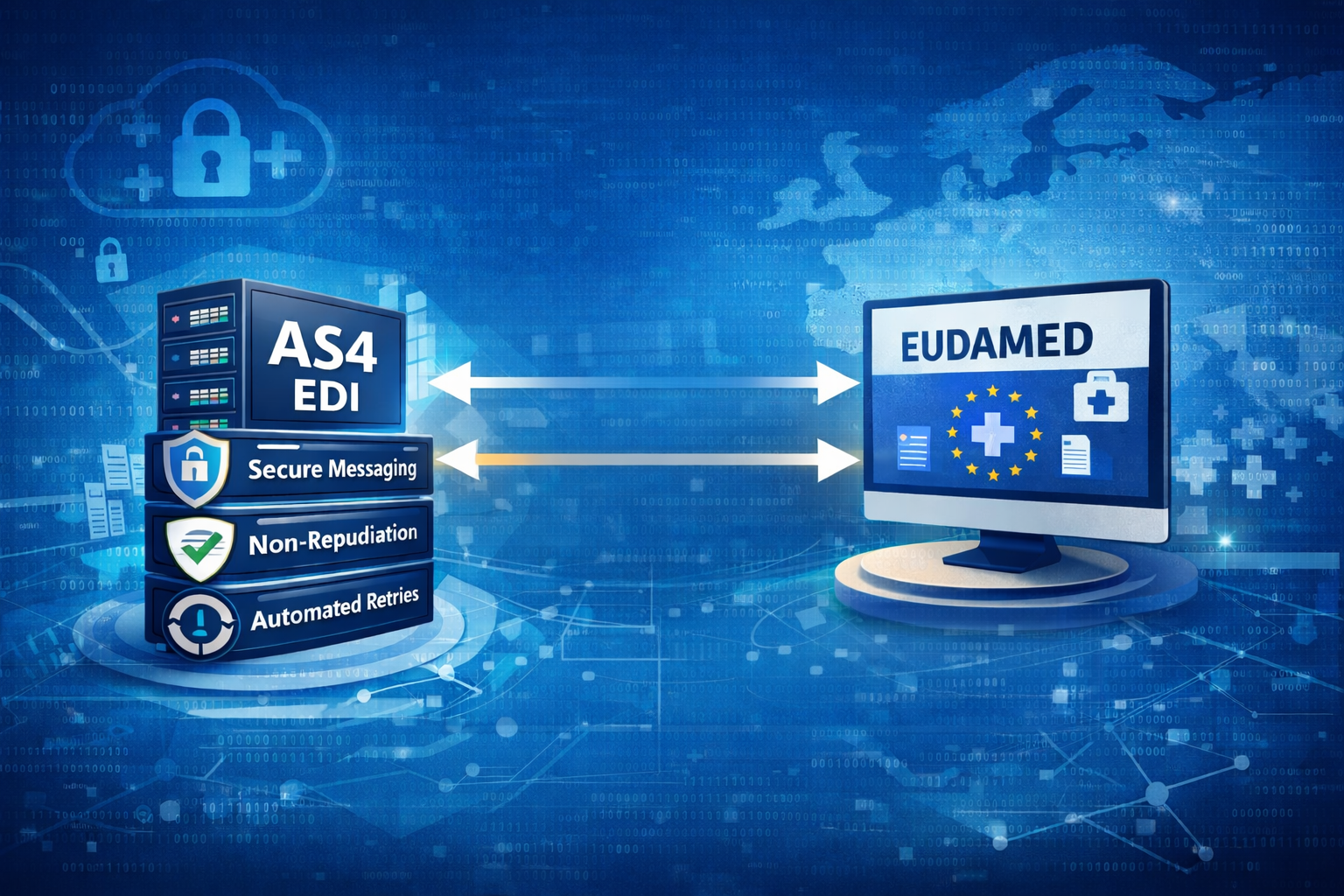
The global healthcare landscape is currently undergoing a structural transition from fragmented, legacy communication protocols toward unified, service-oriented architectures capable of supporting the high-security demands of modern clinical data exchange. Central to this evolution is the Applicability Statement 4 (AS4) protocol, a conformance profile of the OASIS ebXML Messaging Services (ebMS) version 3.0 specification. As healthcare systems in regions ranging from the European Union to Australia and Saudi Arabia seek to digitize their infrastructure, the requirement for a protocol that ensures data integrity, confidentiality, and non-repudiation has become paramount. AS4 has emerged as the preferred standard for business-to-business (B2B) and business-to-government (B2G) interactions due to its payload-agnostic nature and its reliance on the robust Web Services Security (WS-Security) suite.
The Technical Genesis and Standardization of the AS4 Protocol
The development of AS4 was initiated by the OASIS Technical Committee to provide a modern successor to the Applicability Statement 2 (AS2) protocol, which, while successful, was largely confined to document-centric exchanges and lacked the flexibility required for contemporary web services and cloud environments. Standardized in 2013, AS4 represents a simplification of the broader ebMS 3.0 framework, adopting a “just-enough” design principle to lower the barriers to entry for smaller healthcare organizations while maintaining the enterprise-grade reliability required by large-scale national health services.
The protocol is now recognized internationally as ISO 15000-2, affirming its role as a global standard for electronic commerce and administration. Its architecture is built upon the Messaging Service Handler (MSH), which manages the complexities of message transmission, security processing, and receipt generation, allowing internal business applications to remain focused on clinical workflows. This decoupling of transport and application logic is essential for healthcare systems that must integrate a wide variety of heterogeneous IT systems, from laboratory information systems (LIS) to electronic health records (EHR).
Conformance Profiles and Architectural Modularity
One of the defining characteristics of the AS4 specification is its use of conformance profiles, which define the capabilities required for different types of communication endpoints. This modularity ensures that the protocol can scale from high-end gateways in national data centers to light clients in local clinics.
| Conformance Profile | Target Capability | Key Functional Features |
| AS4 ebHandler | Full messaging client and server capability. | Supports both push and pull messaging, 24/7 availability, and complex multi-payload handling. |
| AS4 Light Client | Messaging client only. | Designed for smaller entities; supports pushing data and asynchronously pulling data when a connection is available. |
| AS4 Minimal Client | Basic messaging client. | Limited to core data exchanges; may not support advanced features like multiple payloads or message receipts. |
The ebHandler profile is the most common implementation in national healthcare backbones, such as the European eHealth Digital Service Infrastructure (eHDSI), as it provides the full range of security and reliability features necessary for cross-border data flow. Conversely, the Light Client profile addresses the needs of geographies with spotty internet service or small businesses that cannot maintain a server continuously online, allowing them to participate in the secure network by polling for messages when connectivity is restored.
Core Security Requirements and Cryptographic Foundations
Security in healthcare data exchange is defined by the necessity to protect sensitive electronic protected health information (ePHI) against unauthorized access and tampering during transit. AS4 addresses these requirements through a layered approach that utilizes the WS-Security 1.1 standard to provide end-to-end protection for SOAP messages. Unlike transport-layer security (TLS), which only protects the data while it is moving through a network tunnel, the security features in AS4 are applied at the message level, ensuring that the data remains encrypted and signed even when stored on intermediary servers or routed through a B2B hub.
Authentication and Identity Verification
The AS4 protocol mandates robust authentication mechanisms to verify the identity of the communicating parties. For the ebHandler profile, the use of X.509 digital certificates is the primary method for establishing trust. These certificates are used to sign messages and receipts, providing verifiable proof of origin. In addition to certificate-based authentication, the protocol supports the WS-Security UsernameToken Profile 1.1, which requires the inclusion of a username and a password (often digested) within the SOAP header. This is frequently used for authorizing “Pull” signal requests where a light client must authenticate itself to a server to retrieve pending messages.
Encryption and Data Confidentiality
Confidentiality is maintained through XML Encryption, which allows for the encryption of the entire SOAP body or specific attachments. The OASIS standard specifies that for an implementation to be compliant with the AS4 ebHandler profile, it must support X.509-based encryption algorithms. A critical technical requirement in the protocol is the order of operations: when a message requires compression, signing, and encryption, the payload must be compressed before it is signed or encrypted to ensure that the signature remains valid upon decryption and decompression at the receiving end.
| Security Feature | Specification Requirement | Rationale in Healthcare |
| WSS Version | Support for WSS 1.1. | Ensures modern interoperability and protection against known SOAP vulnerabilities. |
| Signing | Mandatory X.509 Signing. | Establishes non-repudiation; vital for legal proof of clinical transactions. |
| Encryption | Mandatory X.509 Encryption. | Protects patient privacy (ePHI) from unauthorized eavesdropping. |
| UsernameToken | Mandatory for specific signals. | Simplifies authorization for polling and pull-request patterns. |
| Digital Signature Hash | Support for SHA-256 (v2.0). | Modernizes the security posture against collision attacks. |
The Transition to Advanced Cryptography (AS4 2.0)
As cybersecurity threats evolve, the European Commission and other standards bodies have updated the AS4 profile to include more advanced cryptographic algorithms. The eDelivery AS4 2.0 specification, for example, marks a shift toward Elliptic Curve Cryptography (ECC). This version is notably not backward-compatible with previous versions because it adopts incompatible security algorithms designed to meet the “cutting-edge” of security measures. The transition to ECC, including support for the Brainpool curve, allows healthcare organizations to achieve higher security levels with smaller key sizes, which is particularly beneficial for high-volume data exchanges or environments with limited computational resources.
Operational Reliability and Interaction Patterns
The clinical environment requires a level of reliability that goes beyond simple data transfer. AS4 provides a comprehensive framework for “once-and-only-once” delivery, which is critical for ensuring that prescriptions, lab results, and discharge summaries are not lost or duplicated.
Messaging Service Handler (MSH) and P-Modes
The MSH is the functional heart of an AS4 implementation. It is responsible for interpreting the Processing Mode (P-Mode) parameters, which are a set of configuration settings agreed upon by two trading partners. These P-Modes specify everything from the sender and receiver roles to the specific security policies and reliability parameters (e.g., number of retries). By using standardized P-Modes, healthcare organizations can streamline the onboarding of new partners and ensure that all technical parameters are aligned before a single message is sent.
Reliability Mechanisms: Receipts and Duplicate Detection
Reliability in AS4 is achieved through the exchange of Signal Messages, specifically “Receipt” and “Error” messages. When an MSH receives a message, it parses the content and, if successful, returns a signed Receipt. This Receipt serves as proof of delivery and contributes to non-repudiation. If the sender does not receive a Receipt within a specified timeframe, the MSH will automatically retry the transmission according to the P-Mode policy.
Duplicate detection is another cornerstone of AS4 reliability. Each message contains a unique Message ID and a Conversation ID. The receiving MSH maintains a state for these IDs, allowing it to identify and discard duplicate messages that may arrive due to network retransmissions or client retries. This prevents operational errors, such as a pharmacy filling a prescription twice because of a network hiccup.
| Reliability Feature | Technical Implementation | Outcome |
| Acknowledgments | Signed SOAP Receipts. | Legally verifiable proof of successful delivery. |
| Retries | Automatic MSH re-transmission. | Resilience against temporary network outages. |
| Duplicate Detection | Unique Message/Conversation IDs. | Prevention of double-processing of clinical or financial data. |
| Message Ordering | Sequence numbering and state tracking. | Ensures out-of-order messages are processed in the correct logical sequence. |
The Role of AS4 in Regional Healthcare Ecosystems
The adoption of AS4 is often driven by large-scale regional initiatives aimed at fostering interoperability across borders and between diverse healthcare providers.
The European eDelivery and eHDSI Model
In the European Union, the Connecting Europe Facility (CEF) has promoted AS4 as a “building block” for the secure exchange of digital data. The eDelivery AS4 profile is used to power the eHealth Digital Service Infrastructure (eHDSI), which enables Cross-Border eHealth Information Services (CBeHIS). This infrastructure connects National Contact Points for eHealth (NCPeH), allowing Patient Summaries and ePrescriptions to follow a citizen across EU borders.
The eHDSI security model relies on a “circle of trust” established through mutual agreements and the use of the eDelivery AS4 profile. Security is not just a technical requirement but a legal one, governed by the eIDAS regulation, which defines the requirements for secure and reliable electronic documents across sectors. The system incorporates a Gateway service for AS4 messaging, a security module for validating eIDAS tokens, and a pivot transformer that maps national data formats to European Union templates based on the Clinical Document Architecture (CDA) or FHIR.
The Australian Digital Health Agency and “My Health Record”
The Australian Digital Health Agency (ADHA) has implemented modern security standards for its “My Health Record” (MHR) system. While Australia has historically relied on HL7 CDA and older messaging protocols, there is a significant shift toward adopting modern security conformance profiles that align with the Australian Cyber Security Centre’s (ACSC) “Information Security Manual” (ISM).
Healthcare systems connecting to the MHR must demonstrate adherence to the “Essential 8” mitigation strategies and the Privacy Act 1988. The ADHA focuses on ensuring that any software system connected to the national infrastructure incorporates security control functionalities that strengthen its posture against data breaches. The use of AS4 is increasingly seen as a vital part of this landscape, particularly as the country moves toward FHIR Release 5 and the need for more secure, payload-agnostic transport mechanisms for clinical information.
Implementation Challenges and Strategic Considerations
The deployment of AS4 in a healthcare environment is a complex undertaking that requires careful planning across several dimensions.
Certificate Management
The reliance on X.509 certificates and PKI introduces significant operational complexity. Organizations must manage the entire lifecycle of certificates, including issuance, renewal, and revocation. The loss or expiration of a certificate can immediately halt the flow of clinical data, making it essential to implement automated certificate management tools and monitoring.
The Transition Phase and Backward Compatibility
One of the most significant challenges in the move to AS4 is the “migration gap.” Many healthcare partners still rely on legacy AS2 or even email-based communications. Organizations must often maintain dual stacks during a transition period, and in some cases, the new AS4 version 2.0 is not backward-compatible with version 1.x, requiring all participants in a network to upgrade simultaneously. This requires high levels of coordination and “mutual agreement” between clinical partners.
Cybersecurity Risks Beyond Transport
While AS4 secures the transmission of data, it does not address the security of the data “at rest” or the security of the internal systems that produce the data. Healthcare organizations must implement a “holistic security ecosystem” that includes intrusion detection, vulnerability management, and staff training to prevent social engineering or phishing attacks that could compromise the credentials used to access the AS4 gateway.
Synthesis and Strategic Recommendations
The transition to AS4 for healthcare data exchange is a strategic necessity for organizations aiming to provide high-quality, secure, and interoperable care. The protocol provides the essential “non-functional” requirements of a modern B2B standard, security, reliability, and automation, while remaining flexible enough to support the diverse needs of the healthcare market.
To help organizations navigate this transition, we are excited to announce our upcoming Aayu MFT Gateway AS4 service. Our solution is designed to bridge the gap between legacy and modern interoperability by providing robust AS4 capabilities alongside built-in certificate management and continued support for legacy AS2 partners. By removing the technical heavy lifting associated with WS-Security and reliability protocols, the Aayu MFT Gateway ensures your organization remains at the cutting edge of healthcare data exchange. Contact us today for more details on our upcoming release and how we can support your migration strategy.

Talk to an EDI Expert
Join hundreds of organizations already taking full control of their B2B AS2 communications with our trusted solutions. Contact us today to tailor a solution that fits your specific AS2 EDI needs.
Related Articles
View All BlogsExplore our product stack
Try before you buy with a 30-day Free Trial
No commitment, all value. Try the AS2 Solution Risk-Free and discover how our solutions can transform your business workflows. No credit card required.
Explore Your Possibilities
Elevate AS2 Communications with our EDI and AS2 Solutions
See how our AS2 and EDI solutions can simplify your integrations, boost efficiency, and keep you compliant—request a personalized demo today.