Hosted SaaS solution for AS2 and SFTP file transfer. No infrastructure, instant setup.
- Blog
- AS2 and EDI Security; Ensuring Safe Data Transmission
EDI | AS2
AS2 and EDI Security; Ensuring Safe Data Transmission
Security is the paramount concern while implementing the AS2 protocol for Electronic Data Interchange

Sampavi Sriparan
Published: 09 Oct 2023

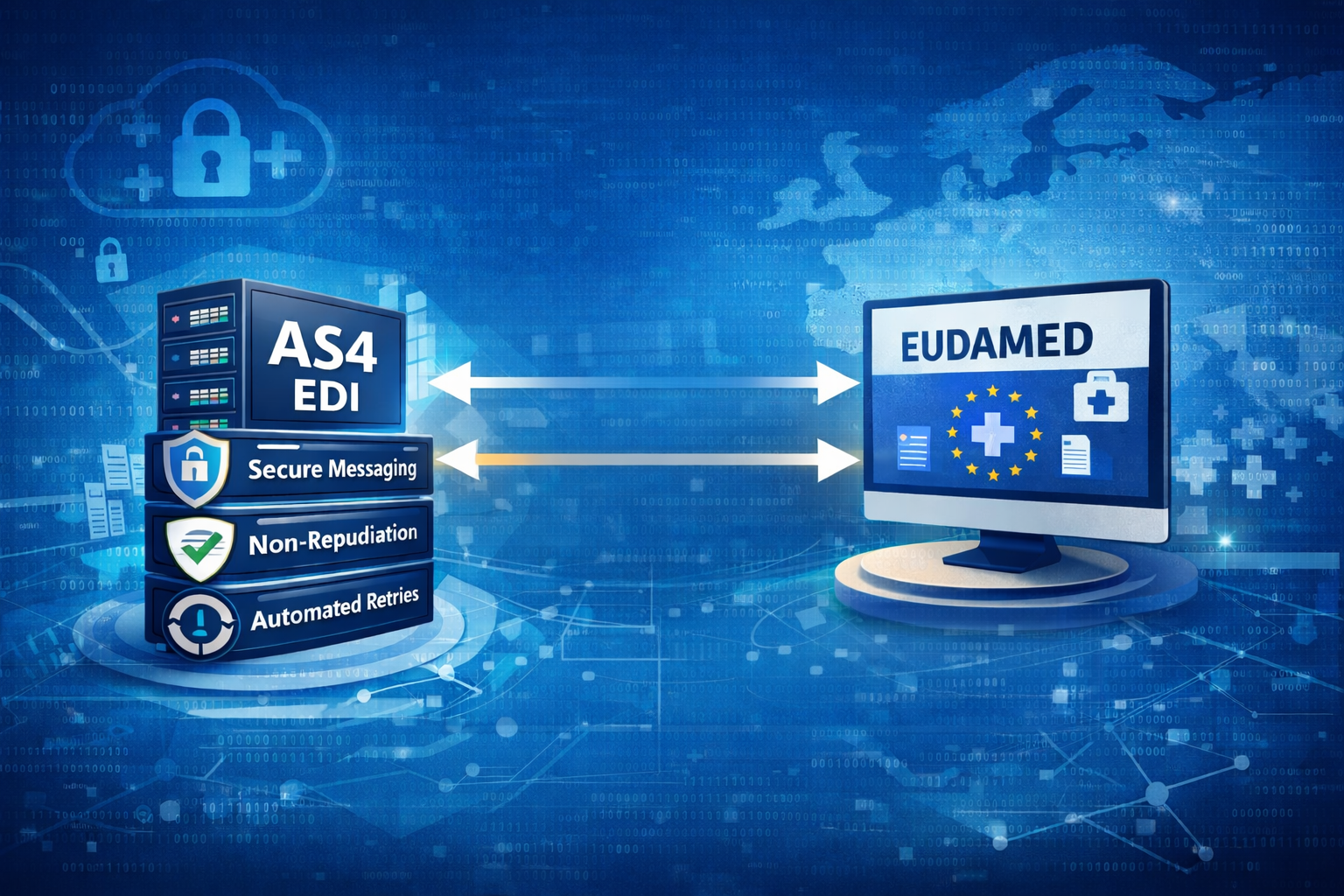
Electronic Data Interchange (EDI) is a standardized technique for exchanging structured and computer-readable business documents such as purchase orders, invoices, and advanced shipment notices between organizations. AS2, which stands for Applicability Statement 2, is one of the protocols widely used for secure and reliable EDI communication over the Internet. AS2 connections provide improved verification and security using receipts, signatures and file encryption. Its transactions and acknowledgments take place instantaneously, enhancing the effectiveness of document exchanges.
AS2 Security features
Security is the paramount concern while implementing the AS2 protocol for Electronic Data Interchange. AS2 includes several key security elements to secure data confidentiality, integrity, and authenticity.
1. AS2 certificates
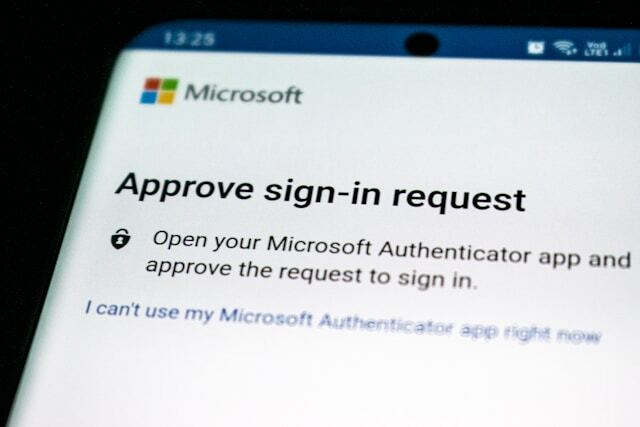
AS2 certificates are essential for securing AS2 transactions by providing authentication, data integrity, non-repudiation, and encryption.These certificates, which are issued by trustworthy firms, are essential for securing the privacy and dependability of electronic data transfer between trading partners or organizations. AS2 certificates are used for digital signatures and encryption, and contain a public key and other identifying information. Digital certificates must be securely managed by the sender and the receiver.
2. Signing
Digital signatures play a significant role in AS2 security by guaranteeing the authenticity and integrity of messages sent between trading partners. Using certificates, AS2 can sign data to verify the sender. Data is signed by the sender using their own private key, which the receiver then verifies using the sender’s public key. Given that only the sender would have access to their own private key, this proves the sender’s identity.
3. Encryption
AS2 uses encryption to secure sensitive information during transmission. Typically, technologies like Secure Socket Layer (SSL) or Transport Layer Security (TLS) are used to encrypt data. Strong algorithms are used to encrypt messages, making it very difficult for unauthorized parties to decrypt the data. The use of AS2 certificates for encryption is also possible. To make sure that only the authorized parties with the associated private key can decrypt and access the content, the sender can encrypt the message using the receiver’s public key.
4. Receipt Acknowledgements
In the AS2 protocol, a partner confirms the successful delivery of a message using Message Disposition Notification (MDN) and Message Integrity Check (MIC).
MDN: In AS2, MDN is a mechanism that sends a receipt to the sender, providing information on the delivery and processing of the message. When the receiver processes the AS2 message after receiving it, they reply to the sender with an MDN. The MDN’s statuses, such as “processed” or “failed’’, reflect how the message processing turned out. The sender can analyze the MDN to verify that the message was successfully delivered and processed.
MIC: To ensure the integrity of the transferred payload, both the sender and receiver independently calculate a MIC value. The receiver shares its calculated MIC value with the sender by including it in the MDN receipt. The sender computes a MIC value when preparing the message. These two MIC values are then compared to ensure that the message sent matches the message delivered, ensuring data integrity.
Nonrepudiation
Digital signatures and receipts are mainly utilized to implement the non-repudiation mechanism in the AS2 security protocol. These mechanisms collectively provide a robust framework for proving the authenticity of messages and ensuring that both the sender and receiver cannot deny their involvement in the message exchange. Digital signatures are used to verify that the document was transmitted by the claimed sender. The receiver’s signature on the returned MDN proves that the message was actually received and also successfully decoded.
Conclusion
AS2 is a specialized protocol designed for secure data exchange over the internet, commonly used for EDI transactions among other types of data exchanges, making it an excellent solution for situations that demand strict security, integrity, non-repudiation, and compliance requirements. The choice of protocol for data transfer depends on specific needs and security considerations. In addition to AS2, other protocols for EDI file transmission include FTP/S and SFTP. Although they can be made safe with the right configuration, the more general-purpose file transfer protocols FTP and SFTP might not offer AS2’s level of integrated security and EDI-specific features.
Find the perfect SaaS EDI-over-AS2 solution tailored to your business needs and enroll in a 30-day free trial.

Talk to an EDI Expert
Join hundreds of organizations already taking full control of their B2B AS2 communications with our trusted solutions. Contact us today to tailor a solution that fits your specific AS2 EDI needs.
Related Articles
View All BlogsExplore our product stack
Try before you commit. 30 days, no credit card needed
Get full access to whichever product fits your needs. Configure real trading partner connections, run end-to-end transactions, and see the platform perform before making any commitment. All three products include a free 30-day trial with no restrictions.
Explore Your Possibilities
Elevate AS2 Communications with our EDI and AS2 Solutions
See how our AS2 and EDI solutions can simplify your integrations, boost efficiency, and keep you compliant—request a personalized demo today.