MFT Gateway is a hosted Software as a Service (SaaS) solution that enables file exchange over the AS2 or SFTP protocol, without the need to install or maintain.
- Blog
- AS2 Message Verification | Expert Guide 2026
MFT
AS2 Message Verification | Expert Guide 2026
Learn how AS2 message verification works with encryption, digital signatures, MIC, and MDNs. Complete expert guide for secure EDI in 2026.

Adeesha Jayasinghe
Published: 30 Mar 2026

Table of Contents
- Technical Framework of the AS2 Protocol and S/MIME Foundations
- The Cryptographic Mechanics of Message Encryption
- Digital Signatures and Authenticity Verification
- The Role of Message Integrity Check (MIC) in Non-Repudiation
- Message Disposition Notification (MDN) Lifecycle and Status
- Managing Identity through X.509 Certificates
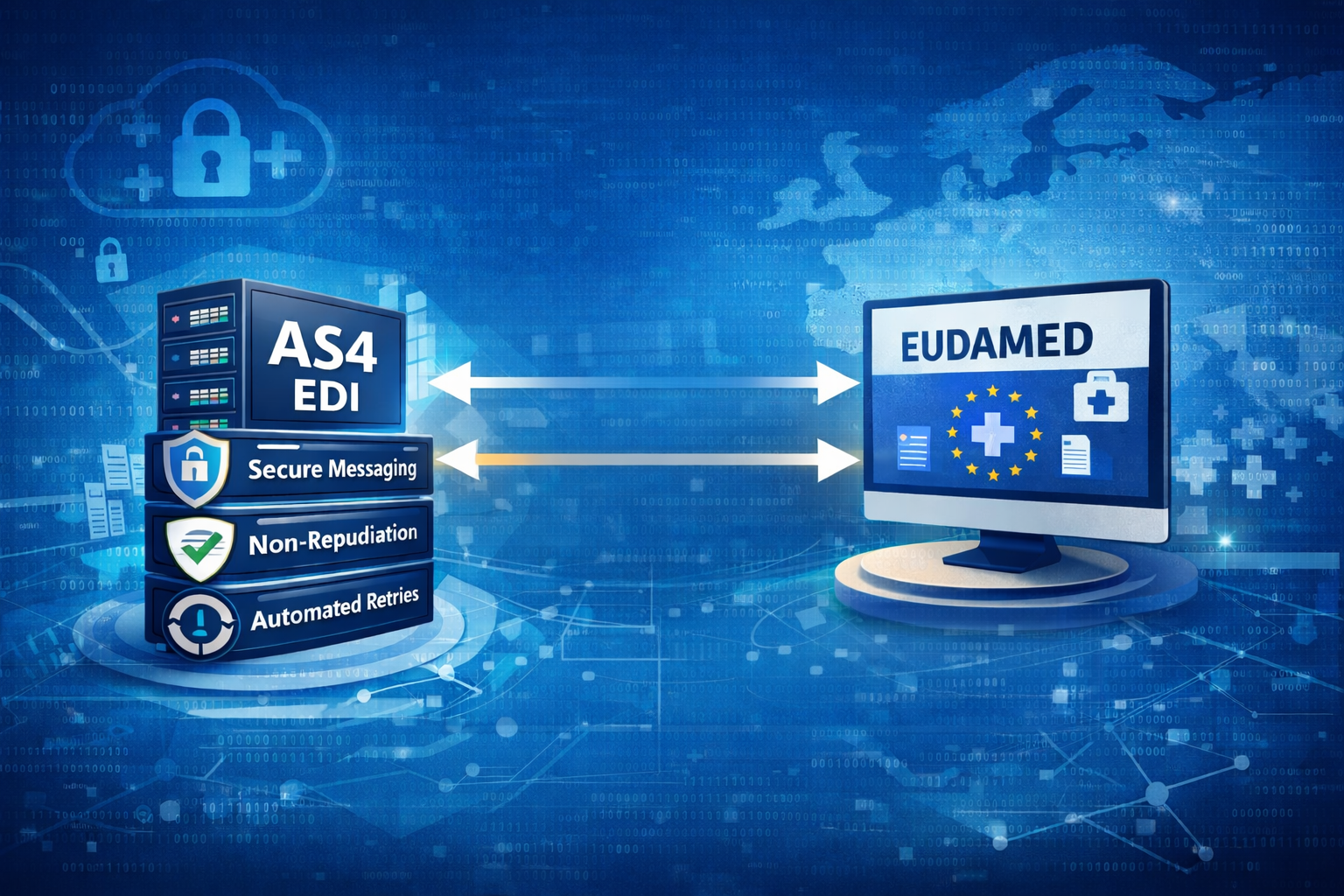
- Troubleshooting Verification Failures
The technical landscape of modern Electronic Data Interchange (EDI) is built upon a foundation of trust, verification, and cryptographic certainty. As organizations transition away from legacy Value-Added Networks (VANs) toward direct, internet-based communications, the Applicability Statement 2 (AS2) protocol has emerged as the definitive standard for secure, reliable, and non-repudiable document exchange. The verification of AS2 messages is not merely a single step but a multi-layered cryptographic process that ensures data confidentiality, sender authenticity, and message integrity. This article provides a comprehensive analysis of the mechanisms governing AS2 message verification, and the implementation of these protocols within the Aayu MFT Gateway platform.
Technical Framework of the AS2 Protocol and S/MIME Foundations
The Applicability Statement 2 (AS2) protocol was developed by the Internet Engineering Task Force (IETF) and codified in RFC 4130. AS2 protocol utilizes the Hypertext Transfer Protocol (HTTP) as its transport mechanism while relying on Secure/Multipurpose Internet Mail Extensions (S/MIME) for its security features. At its core, AS2 provides a framework for wrapping data in a secure envelope that can be digitally signed and encrypted, ensuring that business documents reach their destination in an unaltered state.
The evolution of AS2 was driven by the need for a point-to-point connectivity method that could leverage the cost-efficiencies of the public internet while providing the security and receipt-acknowledgment features historically associated with private networks. Verification within AS2 is achieved through the integration of three primary cryptographic pillars:
encryption for confidentiality, digital signatures for authenticity and non-repudiation of origin, and Message Disposition Notifications (MDNs) for non-repudiation of receipt.
The structural integrity of an AS2 message is defined by its headers and its multi-part MIME body. These headers provide the metadata necessary for the receiving system to identify the sender, determine the intended recipient, and understand the security transformations applied to the payload.
Essential Headers for AS2 Transmission
| Header Name | Functionality | Technical Requirement |
| AS2-From | Identifies the sender’s unique AS2 ID. | Case-sensitive string agreed upon by partners. |
| AS2-To | Identifies the recipient’s unique AS2 ID. | Must match the receiver’s local configuration. |
| AS2-Version | Specifies the protocol version (e.g., 1.0, 1.1, 1.2). | Dictates supported features like compression. |
| Accept-Encoding | Indicates which compression algorithms the sender supports (e.g., gzip) | Useful for saving bandwidth and reducing transmission time. |
| Content-Transfer-Encoding | Specifies how data is encoded for transport. (e.g., binary) | Ensures safe transport without being altered or corrupted. |
| Message-ID | A globally unique identifier for the transaction. | Used for tracking and matching MDNs. |
| Disposition-Notification-To | Requests an MDN | Required for tracking non-repudiation of receipt. |
| Disposition-Notification-Options | Specifies MDN signature and MIC requirements. | Defines the digest algorithm for the receipt. |
| Receipt-Delivery-Option | Specifies the MDN return address for asynchronous MDN delivery | If this header is missing, the MDN is expected synchronously. |
| Subject | Provides a human-readable description. | Useful for debugging and auditing message content. |
| Content-Type | Describes the MIME structure of the payload. | Usually application/pkcs7-mime or multipart/signed. |
The Cryptographic Mechanics of Message Encryption
Encryption in AS2 ensures that the payload remains confidential as it traverses the public Internet. This is achieved through asymmetric key cryptography, involving a mathematically related pair of keys: a public key and a private key. The sender utilizes the receiver’s public key (distributed via an X.509 certificate) to encrypt the message. Only the receiver, who possesses the corresponding private key, is capable of decrypting the content.
If the recipient is unable to decrypt the message, it is often due to a certificate mismatch or an unsupported algorithm. Modern platforms like Aayu MFT Gateway support a wide array of content encryption algorithms, with Triple DES (3DES) and Advanced Encryption Standard (AES) being the most prevalent in professional environments.
Standard Encryption Algorithms in B2B Data Exchange
| Algorithm | Key Length | Technical Assessment |
| AES-256 | 256 bits | Industry standard; highly secure and computationally efficient. |
| AES-192 | 192 bits | Robust security; used in specific legacy environments. |
| AES-128 | 128 bits | Minimum standard for modern secure communications. |
| Triple DES (3DES) | 168 bits | Widely supported legacy algorithm; still common in retail sectors. |
The encryption process typically involves creating an “enveloped-data” MIME part (application/pkcs7-mime), which hides the original payload and any digital signatures from intermediate parties or potential eavesdroppers. Verification fails if the sender uses an incorrect certificate for encryption, resulting in a negative MDN.
Digital Signatures and Authenticity Verification
Digital signatures provide the mechanism for authenticating the identity of the sender and ensuring that the message has not been tampered with. This process establishes Non-Repudiation of Origin (NRO), meaning the sender cannot later deny having initiated the transaction.
The creation of a digital signature in AS2 involves several steps. First, the sender’s AS2 software computes a cryptographic hash (message digest) of the MIME entity to be signed. This digest is then encrypted using the sender’s private key to produce the digital signature. The signature is bundled with the payload, typically using a multipart/signed MIME structure and sent to the recipient.
Upon receipt, the recipient verifies the signature using the sender’s public key. The verification process confirms two critical facts: that the message was indeed signed by the entity possessing the corresponding private key, and that the payload has not changed since the signature was applied. If the verification fails, the recipient knows the message is either not from the claimed sender or has been corrupted during transmission.
Comparison of Signature Digest Algorithms
| Algorithm | Security Strength | Current Industry Application |
| SHA-256 | High | The modern standard for AS2 signatures; recommended for most partners. |
| SHA-512 | Very High | Used in extremely high-security environments; supported by Aayu MFT Gateway. |
| SHA-1 | Moderate | Historically common but being deprecated due to theoretical weaknesses. |
| MD5 | Low | Generally discouraged due to collision vulnerabilities. |
Failure in signature verification often points to a mismatch in the sender’s certificate stored on the receiver’s system, or an untrusted certificate chain. If the sender’s certificate is self-signed, a copy of that specific certificate must be present in the recipient’s trust store to complete the verification.
The Role of Message Integrity Check (MIC) in Non-Repudiation
The Message Integrity Check (MIC) is the cornerstone of the AS2 verification loop. It is a cryptographic digest calculated over the exact MIME entity that is transmitted between the two parties. Depending on how the message is constructed, this may be the signed payload (in the case of signed messages) or the raw payload (if no signature is applied). The MIC ensures that both the sender and the receiver are in possession of the exact same data.
The MIC calculation algorithm is typically specified in the outgoing message headers, specifically within the micalg parameter requested via Disposition-Notification-Options. The receiver, after decrypting the message and verifying the signature, calculates its own MIC of the received content. This value is then included in the Received-Content-MIC field of the returned MDN.
When the sender receives the MDN, they perform a final verification by comparing the MIC returned by the partner to the MIC they calculated and stored before sending the message. A match provides Non-Repudiation of Receipt (NRR), as it proves that the partner received the specific file that was sent, without any alteration.
MIC Verification Logic and Failures
| Verification Scenario | Result | Implication |
| Calculated MIC = Received MIC | Success | Guaranteed message integrity and successful transaction. |
| Calculated MIC != Received MIC | MIC Mismatch | Potential data corruption or incorrect algorithm application. |
| MIC missing in MDN | Verification Incomplete | Receipt lacks cryptographic proof of integrity. |
Message Disposition Notification (MDN) Lifecycle and Status
The MDN serves as the electronic receipt for an AS2 transaction, confirming whether the message was successfully processed or if errors were encountered during decryption or signature verification.
The machine-readable part of the MDN (the message/disposition-notification MIME type) contains the critical metadata for automated verification, including the original Message-ID and the MIC. If the MDN itself is signed by the receiver, it provides the highest level of non-repudiation, as the sender can verify that the receipt truly originated from the intended recipient.
Functional Modes: Synchronous vs. Asynchronous MDNs
The choice between synchronous and asynchronous MDNs depends on the technical requirements of the trading relationship and the size of the files being exchanged. In synchronous mode, the MDN is returned within the same HTTP session as the original message upload. This provides immediate feedback but can lead to connection timeouts for large payloads or slow processing systems.
Asynchronous MDNs are delivered via a separate HTTP connection initiated by the receiver back to the sender’s endpoint URL. This mode is more robust for high-volume environments as it decouples the message receipt from the processing time required to decrypt and verify the content.
Managing Identity through X.509 Certificates
Every AS2 transaction relies on a Public Key Infrastructure (PKI) where identities are validated via digital certificates. A certificate contains the owner’s public key and identity information (Distinguished Name), along with a signature from a trusted issuer.
Certificate Types in the AS2 Environment
Organizations can choose between self-signed certificates and CA-issued certificates. Self-signed certificates are generated locally and are common in AS2 because partners typically exchange connection parameters (including certificates) over trusted channels like encrypted email during the initial setup.
CA-issued certificates are signed by a globally trusted Certificate Authority. These are often required in specific industries, such as the energy sector in Europe, where a centralized trust anchor is mandated. Whether self-signed or CA-issued, certificates must be exchanged prior to message transmission, and any renewal or rotation must be synchronized between partners to avoid verification failures.
Key Store and Trust Store Management
| Store Type | Content | Use Case |
| Key Store | Private key and public certificate (Identity). | Used for signing outgoing messages and decrypting incoming ones. |
| Trust Store | Public certificates of trading partners and CAs. | Used for encrypting outgoing messages and verifying partner signatures. |
Aayu MFT Gateway simplifies certificate management by providing a centralized Certificate Manager. Users can generate new key pairs, create Certificate Signing Requests (CSRs), and import partner certificates with ease. The system also supports scheduling backup certificates to activate at a future date, facilitating seamless rotation.
Troubleshooting Verification Failures
Verification failures in AS2 are often categorized by where in the multi-layered process they occur. A systematic approach to troubleshooting involves examining the Failure Reason field and the MDN status.
Message Send Failures
These errors prevent the initial payload from reaching the partner’s system:
- Connection Issues: The partner’s server may be offline, the hostname is incorrect, or a firewall is blocking the connection.
- Security/SSL Errors: Often indicated by handshake failures between servers, typically caused by a mismatch in SSL certificates.
- Network Errors: Temporary glitches in the network that prevent the transmission from completing.
Negative MDN Received
If the message reached the partner but they returned a “Failed” status in the MDN:
- Decryption Failure: Verify that the correct encryption certificate has been configured for outgoing messages. This often happens if the partner rotates their certificate without notice.
- Signature Verification Failure of the AS2 Message: Ensure you have shared your correct signature verification certificate with the partner.
- MDN Signature Verification Failure: If the partner sends a signed MDN, check the certificate configured for signature verification of incoming receipts to ensure authenticity.
MIC Mismatch and Integrity Errors
This failure occurs when the sender and recipient calculate different Message Integrity Check (MIC) values for the same payload. It typically stems from using different hashing algorithms or discrepancies in MIC format.
Negative MDN Sent
When your AS2 software sent negative MDN for an incoming message from a partner:
- Decryption Failure: Ensure you have shared your correct public encryption certificate with the partner.
- Signature Verification Failure: Verify that you have configured the correct signature verification certificate for that specific partner in your AS2 software.
Async MDN Send Failures
This failure occurs when the system cannot deliver an asynchronous MDN to the endpoint provided in the partner’s Receipt-Delivery-Option header. This is typically caused by network blocking or an unreachable asynchronous endpoint URL on the partner’s side.
The verification of AS2 messages is a fundamental requirement for the secure and efficient operation of the modern digital economy. As global supply chains become increasingly complex and data-driven, the ability to verify every transaction with absolute certainty remains a critical competitive advantage. Aayu Technologies’ suite of tools provides the necessary technical depth and operational simplicity to empower businesses of all sizes to achieve this level of excellence in their AS2 and EDI operations.

Talk to an EDI Expert
Join hundreds of organizations already taking full control of their B2B AS2 communications with our trusted solutions. Contact us today to tailor a solution that fits your specific AS2 EDI needs.
Related Articles
View All BlogsExplore our product stack
Try before you buy with a 30-day Free Trial
No commitment, all value. Try the AS2 Solution Risk-Free and discover how our solutions can transform your business workflows. No credit card required.
Explore Your Possibilities
Elevate AS2 Communications with our EDI and AS2 Solutions
See how our AS2 and EDI solutions can simplify your integrations, boost efficiency, and keep you compliant—request a personalized demo today.