MFT Gateway is a hosted Software as a Service (SaaS) solution that enables file exchange over the AS2 or SFTP protocol, without the need to install or maintain.
- Blog
- Understanding AS4 Message Packaging and Security Layers
AS4
Understanding AS4 Message Packaging and Security Layers
Learn how AS4 message packaging works, including SOAP, ebMS 3.0, and WS-Security layers for secure, reliable B2B data exchange.

Lahiru Ananda
Published: 25 Mar 2026

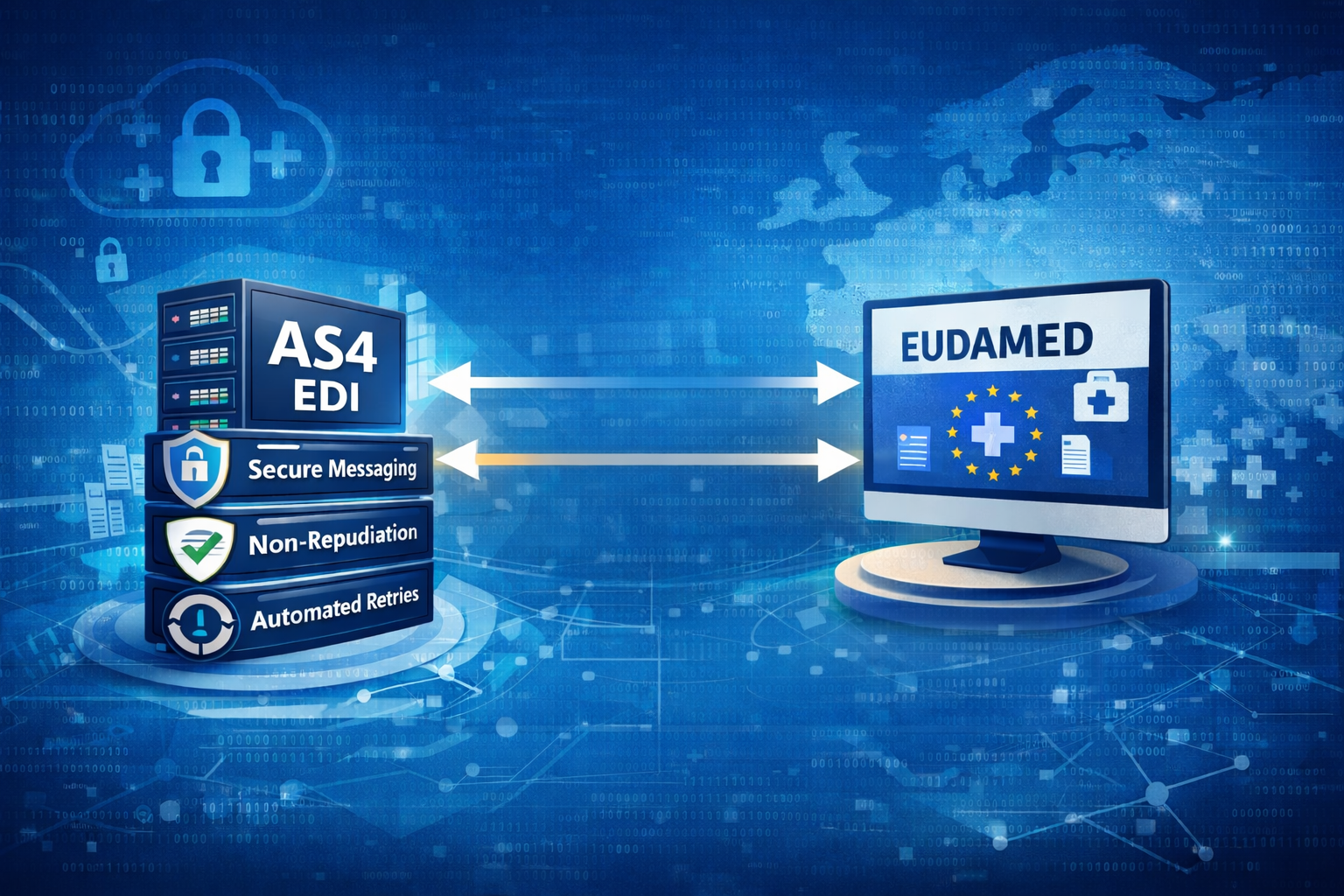
What AS4 Actually Is
AS4 (Applicability Statement 4) is a secure messaging/communication protocol that uses web services standards as a foundation. It is defined by OASIS and is based on an extension of the overall ebMS 3.0 messaging model. The idea behind AS4 is simple:
Send business documents (files, xml data, EDI data, pdf files, anything really!) reliably and securely over HTTP using structured SOAP messages. Under the hood, AS4 builds on a set of web service standards:
- SOAP for structured messages
- WS-Security for encryption and signatures
- ebMS 3.0 for reliability
AS4 is like a shipping container protocol for digital cargo.
The Layered Structure of an AS4 Message
AS4 message is not just a message with some payload. It is actually a multi-layered envelope that ensures the message is not only secure, but also has integrity and reliability.
Here is the conceptual stack, working its way from the outside in:
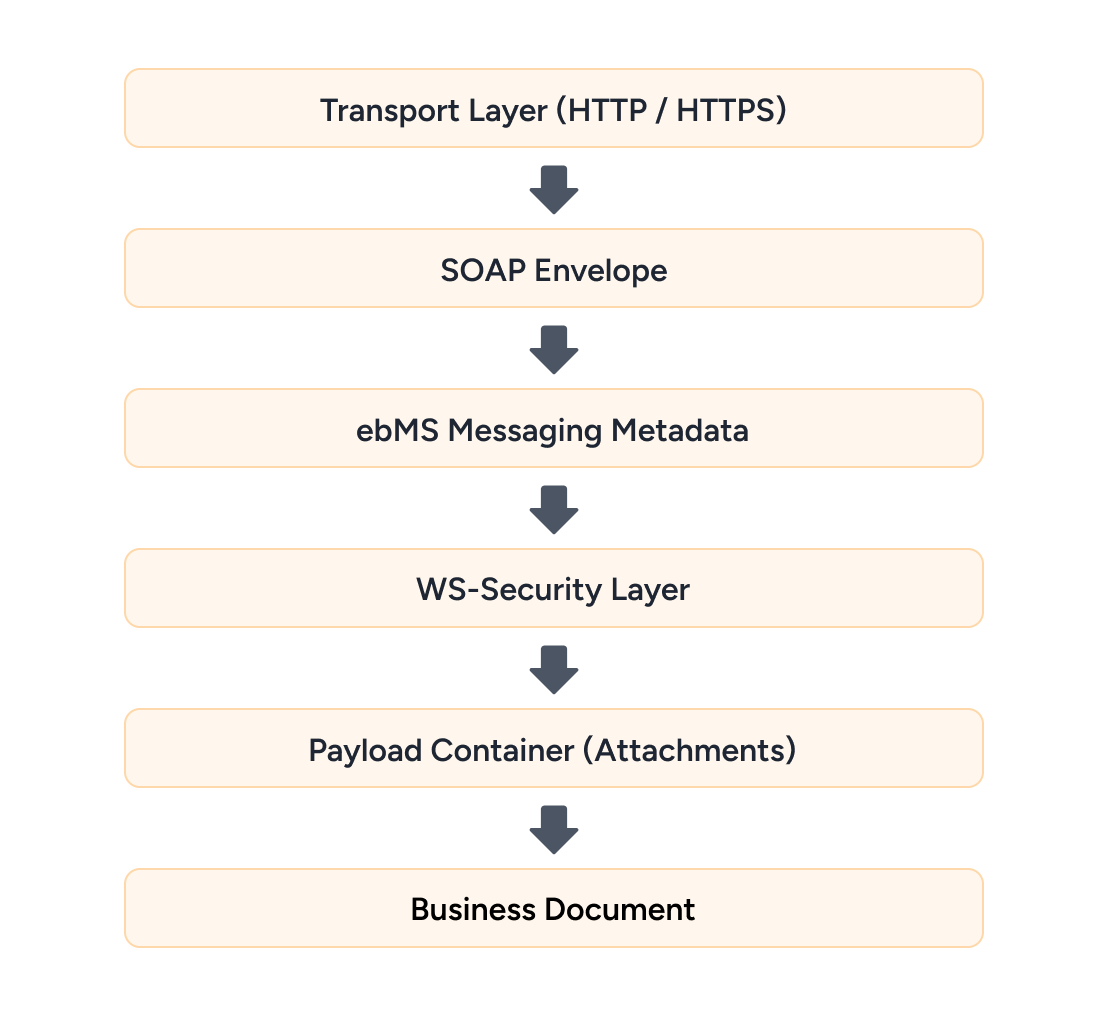
Each layer solves a different problem.
1. Transport Layer
The outermost layer of AS4 messages uses HTTP and HTTPS as their transmission methods. The HTTPS protocol delivers security features such as Transport encryption through TLS, Server authentication and Optional client authentication.
However, transport security alone isn’t enough. The system requires more than transport security because messages can transit through multiple points or they can be stored for later use. Therefore, AS4 implements message-level security through its design which protects the contents of messages.
This is where the next layers come in.
2. SOAP Envelope – The Structural Container
The SOAP envelope, defined by SOAP, acts as the outer wrapper that gives an AS4 message its structure and organization. It functions as a “package format” which maintains correct arrangement of contents that both sender and receiver use to interpret the message without errors.
A simplified structure looks like this:
<SOAP:Envelope>
<SOAP:Header>
Messaging Metadata Security Headers
</SOAP:Header>
<SOAP:Body>
Message Payload Reference
</SOAP:Body>
</SOAP:Envelope>
The <SOAP:Envelope> element at its highest level contains two main components which are the Header and the Body.
The <SOAP:Header> is where all the important control information lives. This section contains ebMS messaging metadata which includes message IDs and sender/receiver details and routing info together with WS-Security elements that include digital signatures and encryption data and security tokens. The section holds critical information which the receiving system needs to understand message processing and sender identification and trustworthiness assessment.
The <SOAP:Body> typically contains references to message payload, which AS4 defines as a payload reference that usually appears as an attachment. This method enables the envelope to maintain its lightweight design while establishing connections to extensive business documents.
3. ebMS Messaging Metadata
The ebMS 3.0 standard defines the ebMS messaging block which operates as the main control hub for AS4 messages within SOAP headers. The payload transmits business content while the metadata describes system procedures for processing message content which needs to be monitored and authenticated with system partners.
ebMS serves as the primary foundation for identity verification and contextual information. The Message ID and Conversation ID elements perform functions of message identification which connects specific messages to complete business procedures such as order processing. The system uses party information to direct messages to the appropriate partners while the Service and Action fields provide the receiving system with information about the message operation type.
The system performs time management functions together with identification functions. Timestamps provide evidence of message currency which blocks replay attacks while reliability parameters establish whether messages need after receipt confirmations or multiple delivery attempts.
This structured metadata system provides essential business functions for enterprises.
- Reliable messaging: Guarantees message delivery through its reliable messaging feature which works in unstable network conditions.
- Message ordering: Ensures messages are processed in the correct sequence (if required by the agreement)
- Duplicate detection: Prevent reprocessing of identical messages.
- Acknowledgements: Verify that the recipient received the message.
- Non-repudiation: Enables users to prove both the message sender and delivery status of the message.
Read more: AS4 Protocol Explained: How ebMS 3.0 Delivers Reliability and Security
4. WS-Security – The Cryptographic Armor
AS4 communication protocol extends its functionality beyond basic transport protection by implementing complete message security through WS-Security. WS-Security provides end-to-end message protection which continues to safeguard data throughout its transmission process and through temporary storage times.
This layer functions through three essential systems:
Digital Signatures
Digital signatures confirm both the integrity of a message and the identity of the person who delivered it. The sender applies their private key to sign selected portions of the SOAP message which includes the message body and essential headers. The receiver then validates this using the sender’s public certificate.
This guarantees:
- Integrity – No tampering during transit
- Authentication – Confirms the sender’s identity
- Non-repudiation – The sender cannot deny sending the message
Signature validation fails when even a single character changes from its original form.
Encryption
Encryption prevents anyone except the authorized recipient from accessing protected information. AS4 encryption typically employs the recipient’s public key for encryption because only the recipient’s private key can decrypt the data.
The scope of the encryption process defines its main importance.
- You can encrypt the entire payload.
- You can select specific elements for encryption which includes sensitive fields.
This provides flexible options which protect confidential information during interception or routing through various systems.
Security Tokens
WS-Security establishes trust relationships between trading partners through the use of tokens which commonly take the form of X.509 certificates. The SOAP header contains these tokens which function during both signature validation and encryption operations.
Security Tokens assists users in solving important inquiries:
- Who sent this message?
- Can I trust this sender?
- Which key should I use to verify or decrypt?
Why Does This WS-Security Layer Matters?
WS-Security enables a zero-trust style model for messaging. The message remains secure even if the transport layer is compromised. The layer together with ebMS metadata provides secure message delivery which maintains reliability and sender-to-receiver verification and protection against unauthorized changes.
Read more: Is AS4 Mandatory? Understanding Global Compliance Requirements
5. Payload Container (Attachments)
The actual business data in AS4 protocol exists outside of the SOAP body because the system transmits business data through attachment methods such as SOAP with Attachments and MIME packaging. These methods break down the message structure into two separate parts which results in better message delivery performance and system expansion capacity.
The SOAP body serves as a reference point that contains a link to the attachment instead of including the actual file. The attachments are sent alongside the SOAP envelope as part of the same HTTP request.
What Can Be Included?
AS4 supports multiple types of payloads which allows different types of data to be transmitted throughout its system. A single message can carry:
- All structured XML documents which include invoices and orders
- EDI files
- PDFs or images
- Any binary data
- Even multiple payloads in one message (e.g., invoice + supporting documents)
Attachments are identified using Content-ID (CID) references, which allow users to access information about each attachment through metadata that includes its MIME type and filename and description.
Why Use Attachments Instead of Embedding Data?
The system design needs to fulfill multiple essential practical requirements:
- Performance: Large files don’t need to be encoded into XML (like Base64), which would increase size and processing overhead
- Efficiency: Enables direct transmission of binary data without any need for conversion
- Scalability: Maintains ability to process extensive data loads without causing SOAP envelope expansion
- Flexibility: Permits users to send multiple connected documents within one message
How It Works in Practice
The underlying structure of the system displays this conceptual organization:
SOAP Envelope
|--- ebMS metadata
|--- WS-Security header
Attachments (MIME Parts)
|--- invoice.xml
|--- order.pdf
The receiving system first reads the SOAP envelope to determine message context and security information and processing rules. The system then uses the SOAP body references to retrieve and process the corresponding attachments.
Security Consideration
Attachments exist under protective measures. AS4 enables attachment signing and encryption through WS-Security which operates the same way as SOAP envelope security. The system guarantees that all external payloads maintain equal message integrity and confidentiality protection throughout their entire transmission process.
The design preserves a clean and light SOAP envelope which lets AS4 manage extensive complex multi-document transfers that businesses need for their actual integrations.
6. The Business Payload
The primary component of an AS4 message consists of its business payload which contains the essential data that organizations need to transmit. The complete AS4 framework operates through its transport system combined with SOAP structure, ebMS metadata and WS-Security elements to safeguard the delivery of the payload.
The payload itself is typically a business document formatted according to agreed standards between trading partners. The data can exist as structured XML or EDI formats or as unstructured binary files which include PDFs and images. Common examples include:
- E-invoices used in financial transactions
- Shipping notices in logistics workflows
- Customs declarations for cross-border trade
- Healthcare records in regulated environments
- Procurement documents like purchase orders
What’s important is that the AS4 protocol establishes neither payload contents nor establishment of payload contents but establishes rules for payload packaging and payload delivery. Industry standards and partner agreements determine the payload’s meaning and its structure.
The business processes of actual systems use this payload as their primary driving force. After validation of the received data it proceeds to ERP systems billing platforms and supply chain tools for processing.
The complicated appearance of AS4 belongs to its real purpose which is to deliver correct data to the proper system while maintaining system security and operational readiness.
Why So Many Layers?
At first glance, AS4 creates an impression of excessive complexity because its multiple layers create unnecessary difficulties for simple file transmission. The actual need for each connecting component exists because businesses use B2B communication systems to handle their complex operational needs. Actual message transmission requires multiple stages because messages must progress through gateways and intermediaries before reaching their destination.
Here’s how the layers map to real problems:
- The secure transport system (HTTPS) provides data protection throughout its network transmission period.
- The structured messaging system (SOAP) enables both systems to comprehend the message format
- The messaging reliability system (ebMS 3.0) guarantees message delivery complete with system failures and message retransmissions
- The authentication system (WS-Security) verifies message trustworthiness by confirming no alterations occurred
- The payload transport system (MIME attachments) enables users to handle large documents or multiple documents through efficient document management
- The network security layer and data structure layer and delivery guarantee layer and trust layer and performance layer function as distinct solutions for various problems.
The current design uses defense-in-depth security measures to protect networks. The system maintains message protection through multiple layers which function as backup security when one protection mechanism fails. The financial industry and healthcare sector and government institutions require data transmission to maintain security standards while allowing complete traceability and compliance verification throughout extended business operations.
Read more: AS4 Protocol in Healthcare 2026: Secure and Reliable Data
Final Thoughts
The AS4 protocol appears complicated at first glance but its various components function to secure business communication throughout international organizational networks. AS4 provides protection through transport security and message-level encryption while ensuring reliable delivery to businesses that operate in environments where data loss and system outages and incorrect data records are not permitted.
Contact us to learn how we can support your AS4 and Managed File Transfer requirements.
Start sending secure AS4 messages in minutes, contact us now.

Talk to an EDI Expert
Join hundreds of organizations already taking full control of their B2B AS2 communications with our trusted solutions. Contact us today to tailor a solution that fits your specific AS2 EDI needs.
Related Articles
View All BlogsExplore our product stack
Try before you buy with a 30-day Free Trial
No commitment, all value. Try the AS2 Solution Risk-Free and discover how our solutions can transform your business workflows. No credit card required.
Explore Your Possibilities
Elevate AS2 Communications with our EDI and AS2 Solutions
See how our AS2 and EDI solutions can simplify your integrations, boost efficiency, and keep you compliant—request a personalized demo today.